The CLI and Forensic Tools
If you’re a Digital Forensic Examiner (DFE), you’re hopefully familiar with Griffeye Analyze DI.
…And, if you you’re a DFE who has to review large amounts of image and Video content in your analysis, I REALLY hope you’re not just familiar with Griffeye, but are a regular user. If so, you may or may not know that Griffeye has a fairly robust CLI (Command Line Interface) that is available if you have an Analyze DI Pro license, or can be purchased separately as a standalone Griffeye Processing Engine without the Full-GUI most are accustomed to.
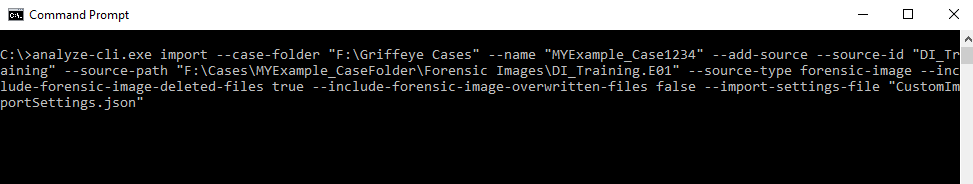
Now you may have hit Command Line Interface and immediately checked out…, but hang with me just a bit longer. Interacting with programs via CLI, can be more complicated yes, however a good CLI also opens the doors to automating some more repetitive tasks, as well as facilitate automating integrations with other tools we may want to use. Anything we can do to streamline and automate some of those simple repetitive tasks, is more time we have to be working on other things.
The CLI Frustration…
Now if you’ve used the command line before whether it be Griffeye, another forensic tool, or just the Windows Command Prompt, you’ve probably spent some time pulling you hair out trying to format the command syntax just-right, while trying to enter long complex file paths. To be fair, it’s a frustration for most people, at some point, and understandable why CLI’s get a bad rap.
…A more approachable CLI
The good news is that an open and document CLI creates a lot of alternate possibilities for how you’d ordinarily work with a tools full GUI version. Scripts and even entirely new Graphical User interfaces with new features can be created that remove the hassle of interacting with the CLI directly. This offers a nice best-of-both worlds option where you can start to explore the CLI, but like the convenience of not having to type out complex paths, commands, and switches.
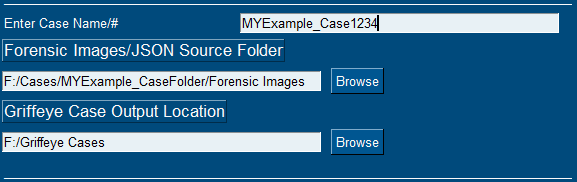
BFIP4Griffeye
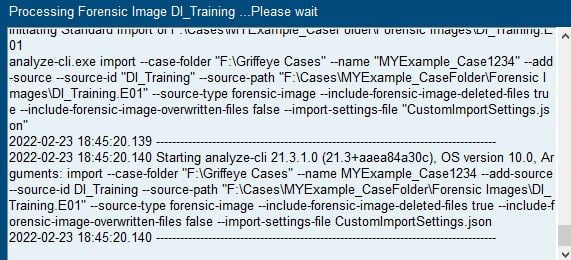
Here’s where Bulk Forensic Image Processer for Griffeye (BFIP4Griffeye) comes in. With this initial public release, BFIP4Griffeye aims to strike at this best-of-both worlds option facilitating a fully GUI driven interface to the Griffeye CLI. Not only does it provide an easy onramp to the CLI, but it leverages some cool automation tricks to speedup the repetitive process of adding several evidence sources to a single case. Just point to the parent case folder containing your forensic images and/or JSON exports, and BFIP4Griffeye will automatically find any supported forensic images/JSON’s, automatically apply a Source ID, and then ingest them into Griffeye. In some situations, this may be no big deal, but when you have a case with A LOT of forensic images to add, this quickly becomes a mundane and time-wasting task.
Currently, the tool allows for seamless case creation, adding of Forensic Images, JSONs, and choice of either the Standard Import or LACE Carver. More features are also in the works and planned for future updates that expose advanced configuration/processing options. In addition, integration with other popular file-carving tools is in the works and will be added soon. This would allow you to elect to use an alternate tool to conduct your file carving, then seamlessly have that data ingested into Griffeye once the carve completes. Which tools/carvers exactly, and how many it supports is still to be decided but if you have any suggestions feel free to submit a feature request. The idea though is that BFIP4Griffeye will be an evolving framework that that will eventually give the user more options for which tools conduct the file carving/recovery phase, then pass that data to Griffeye for ingestion.
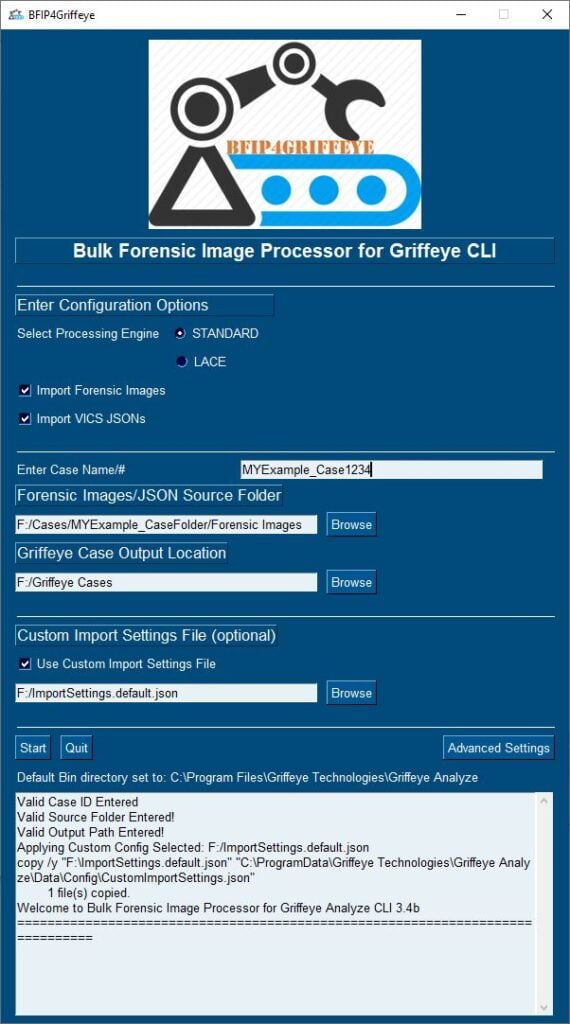
Here’s a quick rundown of the features:

- Current GUI-based mode selection for either Standard Process (allocated files only) or LACE Carver Processing. (Note that LACE does require you have the appropriate Griffeye License available)
- Option to search for and import Forensic Images, JSON packages, or both.
- Bulk ingestion of all forensic images/JSONs by designating the parent folder only that contains them.
- Source ID for Forensic Images are automatically assigned based on name of forensic image file or are extracted from JSON if multiple SourceIDs are stored in JSON.
- Optional use of Custom Import Settings File, for even more granular control over processing options.
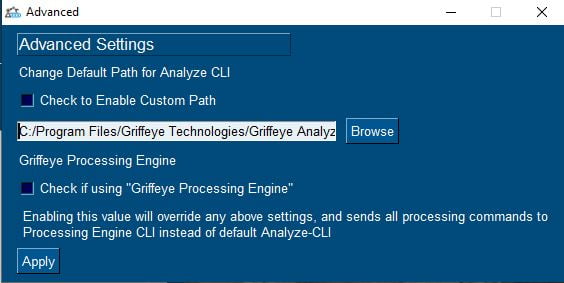
- Advanced Settings to Change default system path for AnalyzeCLI.
- GUI-Integrated console output window with logging and processing feedback.
- Persistent User Settings that dynamically save and fill certain program option/configurations.
Demo Video Coming Soon!
Standard Supported Image Formats:
- .001
- .bin
- .dd
- .dmg
- .e01
- .ewf
- .img
- .iso
- .raw
LACE Supported Image Formats:
- .001
- .ad1
- .bin
- .dd
- .dmg
- .e01
- .ex01
- .ewf
- .img
- .iso
- .l01
- .raw
- .s01
- .vhd
Requirements/Tested on:
- Windows 10/11 – 64bit
- Griffeye AnalyzeDI Pro 21/22 or Griffeye Processing Engine
- Lace processing requires you to have Lace Carver Add-on as part of your Griffeye license
- Important! If using ‘Griffeye Processing Engine’, you must Check the “Griffeye Processing Engine” box under ‘Advanced Settings’ menu prior to starting import.